Overview
Appen Single Sign-On (SSO) feature lets users access their Dedicated instance using one login. SSO can be implemented for contributors via access to the host server (AWS console). Once integrated, Team Admins can invite contributors to Hosted Channels and contributors will be able to directly log into the platform using SSO.
Benefits of Single Sign-On
- Users have fewer passwords to manage and memorize, thereby increasing usage and time savings.
- All established password policies for your corporate network are in effect increasing security for users who have access to sensitive data.
Set-Up Contributor SSO Integration
- Set-up the IDP for contributors:
- Use metadata url: https://<APPLICATION_DOMAIN>/saml-web/v1/saml/metadata?customer_name=contributor-sso
- Use 'single sign-on url': https://<APPLICATION_DOMAIN>/task-force/saml/consume?customer_name=contributor-sso
- Acquire metadata file for this IDP saved as an XML file
-
Access the control plane as root user
-
Currently requires access to the host server and the following command can be used to access the root user:
-
sudo su - root
-
-
- Add metadata for that IDP using the customer_name:
'contributor-sso' with the following command: customer_name = contributor-sso type=file value=<value of path to file> /usr/local/bin/update-vault-saml-metadata.sh
-
Note a confirmation message similar to the following response:
-
Successfully updated metadata for test using file /tmp/test.xml
-
-
On the platform, log into a requester account that is a “Team Admin” of the team you would like to create Hosted Channels for
-
Invite users to desired Hosted Channel(s) via bulk CSV upload or individual input
-
Note: All contributors must be invited before they can use SSO
-
-
Confirm contributors are uploaded and under a “Pending” state
-
Contributors should now be able to sign-in via SSO and access their designated Hosted Channels
-
Once a contributor logs in via SSO for the first time, their “Pending” state should update to “Accepted”
For the field formats, please see below for an example of an Okta application setup. Please note these fields are specific to Okta integration and may differ for other IDP services.
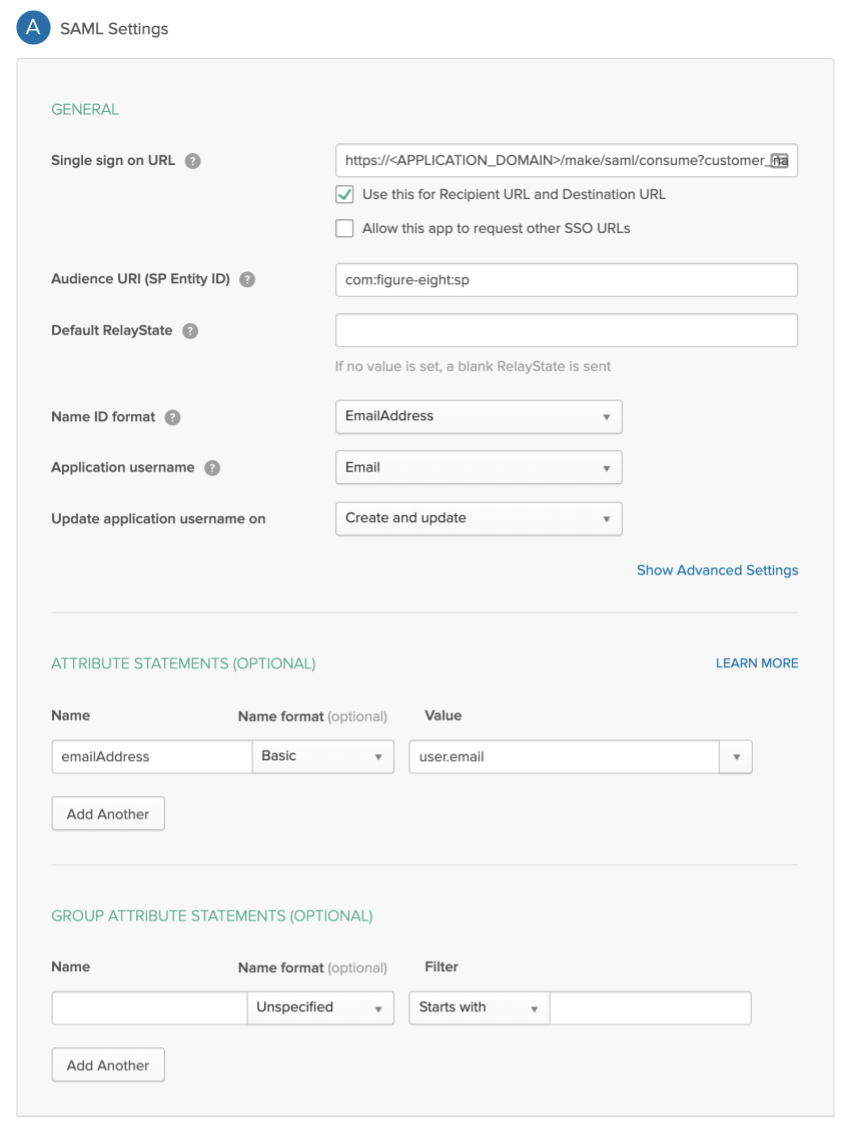
Fig 1: Example Okta Application Set-up
For the Single sign-on URL, use one of the URLs given above as appropriate. The key fields of interest which must be correct are:
- Audience URI: 'com:figure-eight:sp'
- Name ID format: 'EmailAddress'
- Application username: 'Email'
- in Attribute Statements: Name: 'emailAddress', Name format: 'Basic', Value: 'user.email'
The rest of the fields can be left as-is.
How to Add Contributors via SSO
1. After setting up the SSO integration via the host server, new contributors should be invited to desired hosted channels by Team Admins.
2. Confirm each contributor is in a “Pending” state. Contributors should not attempt to sign in until they are invited to a hosted channel.
3. Once in a "Pending" state, contributors will be able to SSO directly into the platform. Contributors do not need to "Sign Up" via [custom domain]/task-force.
4. Once logged in, the contributor will be able to access all hosted channels they were invited to.
5. The Team Admin can confirm success per the “Accepted” contributor state on the Hosted Channel page.